Devin Johnson wrote:
The ClearFoundation & ClearCenter are pleased to announce a great new addition to the ClearOS Marketplace. Introducing: Attack Detector.
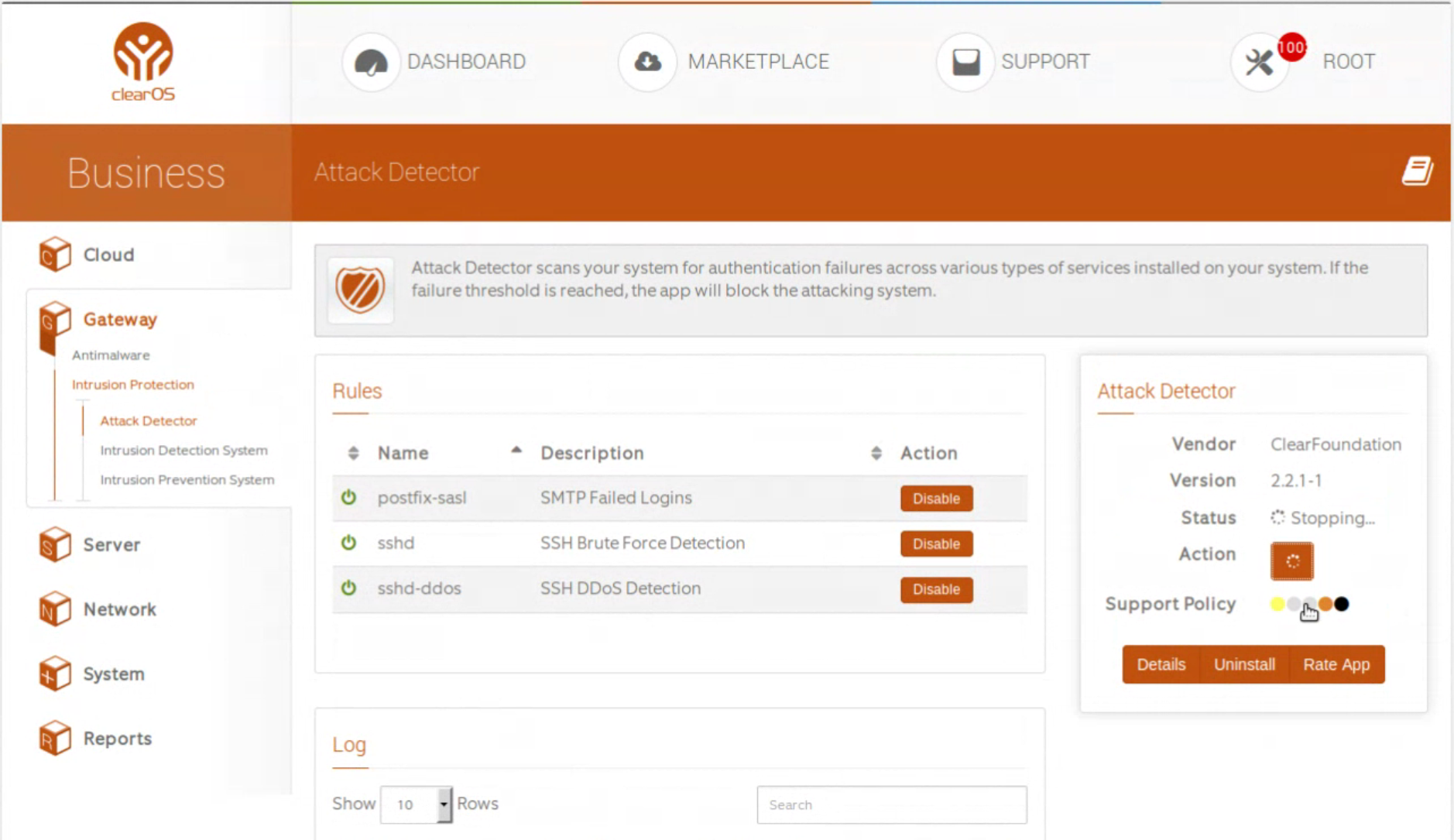
The Attack Detector app scans your system for authentication failures across various types of services installed on your system. If the failure threshold is reached, the app will block the attacking system. For example, it is a common tactic for spammers to guess a valid username/password combination for sending unsolicited outbound mail. The Attack Detector detects the failed login attempts and actively blocks the spammer.
Multiple apps in Marketplace will provide rule sets for the Attack Detector app, such as the SSH Server app, FTP Server app and more. This app will function as a standalone app, however it may also be combined with the Intrusion Detection System & Intrusion Prevention System apps to provide maximum protection against attacks.
For more information CLICK HERE.
LINK to the original announcement.
Share this post:
Responses (14)
-
Accepted Answer
HI Peter,
i posted my issue in https://sfj48-fkj200.heiksthsd.cf/clearfoundation/social/community/app-attack-detector-no-rules-clearos-7-2 and replied to your advice in that post with the issues i am having since this is marked as resolved and my issue is not resolved. -
Accepted Answer
-
Accepted Answer
Hi Loren and Nick,
The fail2ban filter definitions are indeed in /etc/fail2ban/jail.d, however, it is the related app that pulls in those definitions. For example, the /etc/fail2ban/jail.d/clearos-postfix-sasl.conf configlet that detects SMTP authentication failures is part of the SMTP Server app. You won't see that fail2ban filter in the ClearOS web interface unless the SMTP Server app is installed.
But here's a bit of a head scratcher -- you should at least see a couple of SSH related fail2ban filters. The SSH Server app is installed by default and the latest version of that app includes a couple of fail2ban configlets. -
Accepted Answer
If it is anything like a standard fail2ban, my /etv/fail2ban/jail.d is empty as well. Configuration is normally done through changing /etc/fail2ban/jail.local if ClearOS has been good or /etc/fail2ban/jail.conf if not. Similarly the filters and actions are in /etc/fail2ban/filter.d/ and /etc/fail2ban/action.d/. The filters and actions conventionally follow the jail names. The jails themselves end up as iptables chains. -
Accepted Answer
Hi, I installed on Home 7.2 but it is an upgraded system from 7.1, not a clean install. Attack Detector app Version 2.2.4-1 and it is not showing any rules in the webgui so i sshed into my clearos and checked etc/fail2ban/jail.d/ with ls -lsa and the only thing showing is 00-firewalld.conf. is there a way to manually install rules? i have tried removing and re installing the app through the marketplace and still showing the same so i removed it again and tryed installing via yum install fail2ban --enablerepo=clearos-centos,clearos-epel,clearos-centos-updates then yum --enablerepo=clearos-centos,clearos-epel,clearos-centos-updates,clearos-updates-testing install app-attack-detector and it is still showing only 00-firewalld.conf in the jail.d. anyone got any ideas on how to fix this issue? -
Accepted Answer
-
Accepted Answer
-
Accepted Answer
Hi,
I had already Fail2ban installed a long time ago. Attack-detector app installed with no problem on 7.2 Home. All is working correctly except one thing: in the log, i've a lot of banned IP exceeding my ban limit (86400s = one day). After looking in the code of this app, it seems that the IP showing in the log are grepped on fail2ban.log only for the word 'BAN' so the IP UNBANed are not deleted.
I know it's only 'cosmetic' as fail2ban is working correcly, it unbans those IP after the limit.
Clearos please continue your excellent work.
Sorry for my english (I'm French and a long time user of your distribution (I think, I began with COS 3; was a long time ago ;-)) -
Accepted Answer
-
Accepted Answer
-
Accepted Answer
-
Accepted Answer
Please login to post a reply
You will need to be logged in to be able to post a reply. Login using the form on the right or register an account if you are new here.
Register Here »